You are looking at the documentation of a prior release. To read the documentation of the latest release, please
visit here.
New to Voyager? Please start here.
Monitoring Voyager operator
Voyager operator exposes Prometheus ready metrics via the following endpoints on port :8443:
/metrics: Scrape this to monitor operator.
Follow the steps below to view the metrics:
- Give
system:anonymoususer access to/metricsurl. This is not safe to do on a production cluster.
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRole
metadata:
name: appscode:system:metrics-collector
rules:
- nonResourceURLs: ["/metrics"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: ClusterRoleBinding
metadata:
name: appscode:system:metrics-collector
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: appscode:system:metrics-collector
subjects:
- apiGroup: rbac.authorization.k8s.io
kind: User
name: system:anonymous
$ kubectl auth reconcile -f docs/examples/monitoring/metrics-collector.yaml
clusterrole.rbac.authorization.k8s.io "appscode:system:metrics-collector" reconciled
clusterrolebinding.rbac.authorization.k8s.io "appscode:system:metrics-collector" reconciled
- Now, forward the port
:8443to your workstation.
$ kubectl get pods -n voyager | grep voyager
voyager-operator-f89dcccdb-plvmt 1/1 Running 0 27m
$ kubectl port-forward -n voyager voyager-operator-f89dcccdb-plvmt 8443
Forwarding from 127.0.0.1:8443 -> 8443
Forwarding from [::1]:8443 -> 8443
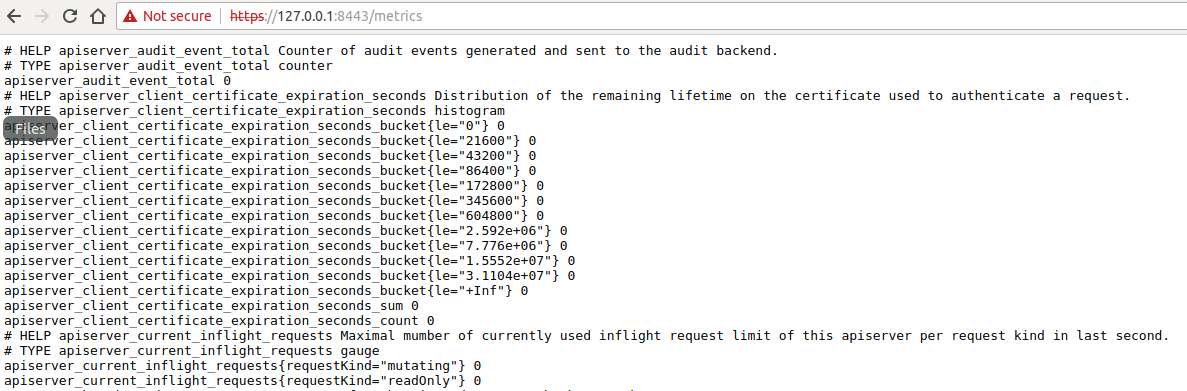
- Now, visit the url: https://127.0.0.1:8443/metrics
- Once you are done, remove access to
system:anonymoususer.
$ kubectl delete -f docs/examples/monitoring/metrics-collector.yaml
clusterrole.rbac.authorization.k8s.io "appscode:system:metrics-collector" deleted
clusterrolebinding.rbac.authorization.k8s.io "appscode:system:metrics-collector" deleted